By Rachael Stickland and Leonie Haimson, co-chairs, Parent Coalition for Student Privacy
High schoolers hate waking up early on Saturday mornings, especially to take high-stakes tests like the College Board’s SAT or the ACT. Next Saturday, January 23, 2016 marks the last time that U.S. students are able to take the current SAT before the new test comes online on March 5.
Anxiety over the “new” test has left many families scrambling to get their kids registered for the older, well-established version to be administered in just a few days. Now that the day is almost near – training courses and practice tests completed – there’s one last thing parents must do to help their children prepare for Saturday: advise them not to answer the optional pre-test questions.
Just moments before administration of the exam officially begins, or upon registering online, students may be asked to answer questions on a student questionnaire and to check off a box agreeing to participate in the Student Search Service ™ program if they want to receive information from colleges or scholarship organizations. See below or here for more information:
According to POLITICO, “Depending on the exam, at least 65 percent — and as many as 85 percent — of test takers check that box, according to the College Board and ACT. Parents do not have to give their consent, as this is only required by federal law while collecting personal data from children under 13.”
Students will be asked their Social Security number; other questions may include their grade point average, religious affiliation, ethnicity, family income, interests, citizenship, disabilities, and more. Under immense pressure to perform well on the test, and often not aware that answering these questions is fully voluntary, students may be enticed to offer up this information, especially if they believe it will increase their opportunity to be recruited by elite colleges or offered scholarships. They may not even realize that this information may be used to help colleges decide who not to recruit or admit as well. As the College Board puts it,
As part of taking a College Board exam, students are asked to fill out a student data questionnaire…. Participating, eligible organizations can then search for groups of students who may be a good fit for their communities and programs, but only among those students who opt to participate in Student Search.
The search criteria can include any attribute you provide, except the following: disability, self-reported parental income, social security number, phone numbers and actual test scores. The most searched items are expected high school graduation date, cumulative GPA and intended college major.
And: By opting in, they give the College Board permission to share their names and limited information with colleges and scholarship programs looking for students like them.
In other words, colleges are looking not just for students to recruit but who to admit and/or reject; or as the College Board softly frames it, those “who may be a good fit for their communities and programs.”
What your weary-eyed, college-bound children may not also realize is that when they provide the College Board or ACT personal details, their “profiles” are not simply “sent” to interested parties, rather they are sold for as much as 40 cents apiece in the shadowy data market.
According to the College Board website: “During the registration process, we ask students for: name, address, date of birth, gender, Social Security Number or student ID, and address. We may also ask for phone numbers and email addresses, school name, grade level or expected graduation date, ethnicity, and a parent’s name, email address, and education level.”
And: “…we ask students for personal information to help them make choices about their future. To help students receive the most relevant and accurate information about their college options and scholarship opportunities through Student Search Service®, we also ask optional questions about academic and extracurricular interests, career and field of study interests, family income, and religious preferences. Students must opt in to participate in this service; the College Board does not include students without their consent. Students may also opt out at any time.
Note that link above, in case you or your child have already opted in upon registration that you still have the right now to opt out. The information requested varies by the exam they are taking, with the most intrusive data being asked of students when taking the SAT and PSAT, including religion, ethnicity and grades and citizenship, while less intrusive information is asked of students taking AP exams. See here for the differences.
Some parents may find this practice acceptable, especially if they perceive that their children “may” benefit when their information is passed along – or they may not. But what is also objectionable is that the College Board and ACT refuse to tell students (or parents for that matter) that they SELL the information. According to POLITICO, ACT’s profits generated from selling student profiles were approximately $15 million in 2012; the College Board wouldn’t disclose its revenue from its trademarked Student Search Services ™ program but it surely was many millions as well.
At one place on its website, College Board falsely claims it doesn’t sell student data. On its “privacy policy” page, many parents will read the following: “The College Board does not sell student information. Students can voluntarily opt in to our Student Search Service. Qualified colleges, universities, nonprofit scholarship services, and educational organizations pay a license fee to use this information to recruit students and manage enrollment in connection with educational or scholarship programs.”
What the difference is between selling student data or selling “a license fee” to colleges and organizations to receive the data is a difference without a difference.
On another page, the company adjusts this claim by saying only that it doesn’t sell student data to test prep companies – not mentioning colleges or other organizations: “It is the College Board’s strict policy NOT to sell student information to test-preparation companies, nor are such companies affiliated with the College Board.”
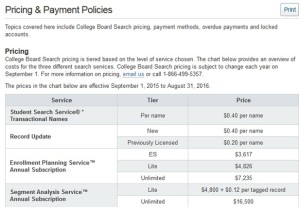
On a yet a different page, meant for its institutional clients, the College Board makes clear that it does indeed sell student data, at 40 cents per name, and offers high priced subscription services for “enrollment planning”:
See the Pricing and Payment Policies here:
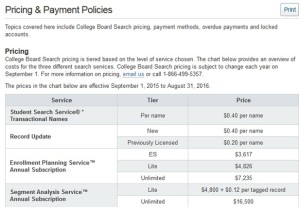
The Enrollment Planning Service, according to the College Board “precisely locates students — both within the United States and abroad — who meet admission criteria and are likely to succeed at a particular institution. Enrollment Planning Service also informs better and more-strategic recruitment activities based on a wide range of criteria including geography, demographics, academic preparation and educational aspirations.”
Its “Segment Analysis Service™ (formerly Descriptor PLUS™) is a powerful data enrichment service that allows admission professionals to identify promising prospective students by learning more about where they live and where they go to high school. Segment Analysis’ Educational Neighborhood and High School Cluster tags leverage data on millions of students and thousands of high schools to provide a more complete picture of various student segments and help you align your recruitment efforts to the characteristics of these segments.”
College Board adds that the Segment Analysis Service allows institutions to “achieve better yields from admission through graduation,” presumably in the effort to boost their four year graduation rates.
This is not to let off the ACT off the hook. ACT subjects parents and students to an even more detailed and intrusive survey on their website, with detailed questions about a student’s disabilities, preferences, religious practices, hobbies and more.
According to POLITICO, the ACT also lets customers filter student profiles by family income, parents’ education levels and student disabilities.
As first reported by an independent educational consultant Nancy Griesemer, the ACT even sells an algorithm to colleges based upon a student’s personal data points to help them decide whom to admit – without informing parents or students how this information may be used:
“… assessments [are] provided to approximately 450 institutional participants in ACT Research Services of “Overall GPA Chances of Success” in various general categories of majors including education, business administration, liberal arts, and engineering, as well as “Specific Course Chances of Success” in broad areas such as freshman English, college algebra, history, chemistry, psychology etc.
Chances of success are made in terms of those students likely to receive a “B” or better in these areas or those students likely to receive a “C” or better. And they are nowhere to be found on the ACT report provided to students and families.”
Why the secrecy? Why the deception? If you find this outrageous, you’re not alone. As far back as 2011, the data collection and storage practices, as well as the commercialization of student information, by College Board/ACT spurred Congressional inquiry.
A lawsuit was filed against the College Board and ACT in 2013 (Spector v. ACT, Inc. et al) and another in 2015 (Silha v. ACT, Inc. and the College Board), for deceptive practices, in that they never disclosed to students that their data was being sold as opposed to freely “shared.”
Unfortunately, the first lawsuit was voluntarily dismissed by the plaintiff in 2014, and the second lawsuit was recently dismissed when the Judge ruled that the plaintiffs failed to make their case showing any harm to the students from the sale of their data.
A Parent Coalition for Student Privacy researcher, Cheri Kiesecker, recently wrote the College Board to ask if students chose to NOT complete the survey, would their college admission chances be affected. See the reply from SAT / College Board here. Their representative responded that if a student does not opt in to Student Search Service ™, ”it will not impact their chances at being accepted into colleges or scholarship programs in any way.” What the representative did not say that if they opt in, it may negatively affect their application or scholarship opportunities.
So what should you say to your children if you’re a parent concerned with their privacy?
On its website, the College Board offers a “Test Day Checklist,” including what to bring (i.e. photo ID) and what to leave at home (i.e. cell phone) on test day. The same website links to the College Board’s Student Search Services ™ data-selling program where it reminds test takers to check the box to opt in when you take the SAT. (See the screenshot below.)
Use this information to educate your children. Explain to them why it’s important to never share personal information that is not absolutely necessary to register for or take the test. Advise them not to share their Social Security number or any other information that is not required. Show them the screenshot to see what the search consent checkbox may look like and how to answer. Then use our handy checklist to get yourself ready for the big test on Saturday.
And remember … once the test is complete, encourage your children to research colleges and scholarships on their own that might be a good fit for them. Their personal information doesn’t have to be sold– and should never be offered unknowingly in a manner that could limit their opportunities.
Parent Coalition for Student Privacy’s SAT Pre- Test Day Checklist:
1. On Thursday or Friday, talk to your children about the importance of providing only the personal information necessary to take the test, and show them the SAT’s Student Search Service ™ screenshot below so they know what it might look like and which box to select (No, thanks.);
2. Encourage them to go to bed early Friday night, get plenty of rest, and set the alarm (AM, not PM!);
3. Serve a nutritious breakfast Saturday morning to your children and remind them to bring a photo ID, the “admission ticket,” NO. 2 pencils and an acceptable calculator from the College Board’s Test Day checklist;
4. Remind them NOT to volunteer any personal information other than what is required like name, address, school, date of birth, etc., and that there is no reason to offer up their Social Security number, religious affiliation, family income, or other extraneous information. They should also CHECK the “No, thanks” box if there is one in the Student Search Service ™ section.
5. Reassure them to relax and just do their best on the exam itself.